CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right tool.
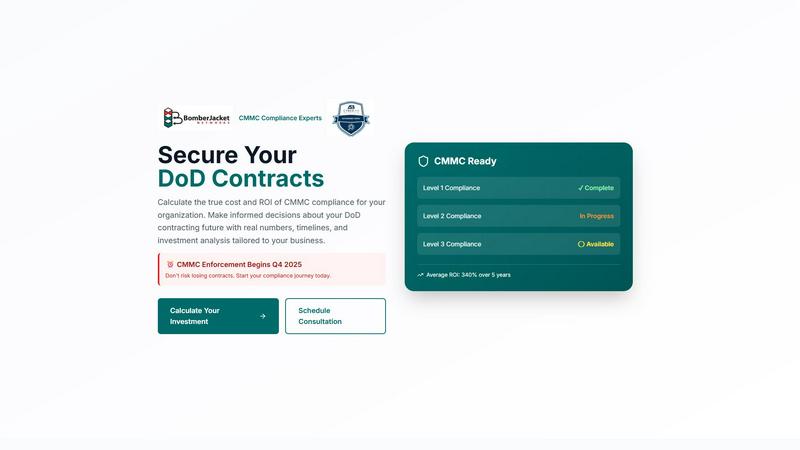
CMMC ROI
Calculate your CMMC compliance ROI to confidently secure DoD contracts and guide your investment decisions.
Last updated: March 1, 2026
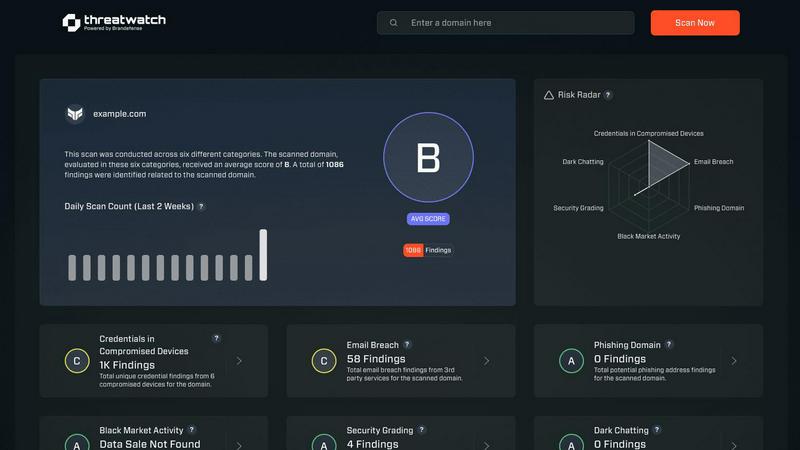
Threat Watch
Threat Watch identifies security vulnerabilities and offers immediate solutions to enhance your cybersecurity health.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Comprehensive Cost Analysis
CMMC ROI offers a detailed breakdown of the total investment required for CMMC compliance. It takes into account implementation costs, ongoing maintenance, and recertification expenses, providing a clear picture of the financial commitment involved over a five-year period.
ROI Calculation
The tool computes a precise return on investment by analyzing protected contract values, avoided breach costs, and competitive advantages. This calculation helps businesses understand the potential financial benefits of achieving compliance, making it easier to justify expenditures.
Personalized Scenarios
Users can input their unique company metrics, such as size, annual revenue, and current compliance status, to generate customized ROI scenarios. This feature allows contractors to see how their specific circumstances impact costs and returns, enabling more informed decision-making.
Strategic Planning Support
CMMC ROI provides insights into the strategic value of compliance, including projected win rates and contract protection. By understanding these dynamics, contractors can better position themselves in the competitive DoD contracting landscape and mitigate risks associated with non-compliance.
Threat Watch
Continuous Vulnerability Assessment
Threat Watch offers real-time assessments of your organization's vulnerabilities, ensuring that you are always aware of potential weaknesses before they can be exploited. This feature helps in maintaining a proactive security posture.
Dark Web Monitoring
Stay ahead of cybercriminals with Threat Watch's dark web monitoring capabilities. This feature continuously scans for exposed credentials and compromised accounts, alerting you immediately if sensitive information is found, thereby mitigating associated risks.
Automated Risk Prioritization
Instead of manually sifting through alerts, Threat Watch automatically prioritizes risks based on their severity and potential impact on your organization. This allows security teams to focus on the most critical threats first, enhancing overall response efficiency.
Comprehensive Security Health Dashboard
The solution includes a user-friendly dashboard that provides a clear and actionable overview of your cybersecurity health. With visual insights into key security categories, stakeholders can make informed decisions quickly.
Use Cases
CMMC ROI
FCI Contractors
For small contractors dealing with Federal Contract Information (FCI) that need Level 1 compliance, CMMC ROI calculates the investment required and illustrates the financial benefits of achieving and maintaining compliance, ensuring that they remain competitive in the market.
Small to Medium-sized Contractors
CMMC ROI helps small and medium contractors understand the investment needed for Level 2 compliance. By showcasing potential returns, it allows these businesses to make strategic decisions that align with their growth goals and compliance requirements.
Large Contractors
Large prime contractors facing Level 3 compliance can utilize CMMC ROI to assess the significant investments involved. The tool highlights the high cost of non-compliance, helping these businesses prioritize their compliance efforts while also illustrating the long-term financial benefits of investing in cybersecurity.
Technology Firms
CMMC ROI is valuable for technology firms with DoD contracts that require compliance at various levels. By using the tool, these firms can analyze their specific scenarios, ensuring they allocate resources effectively to meet compliance standards while maximizing potential returns.
Threat Watch
Proactive Threat Mitigation
Organizations can utilize Threat Watch to identify and address vulnerabilities before they are exploited. By continuously monitoring assets and providing actionable insights, security teams can implement fixes and updates in a timely manner.
Incident Response Enhancement
In the event of a security incident, Threat Watch equips teams with the essential data needed for effective incident response. By offering detailed analyses of threats and their origins, the tool helps in crafting a swift and informed response strategy.
Risk Management Reporting
For risk managers and executives, Threat Watch provides comprehensive reporting capabilities. These reports highlight critical vulnerabilities and overall security posture, enabling better risk management decisions and resource allocation.
Compliance Assurance
Organizations in regulated industries can leverage Threat Watch to ensure compliance with various cybersecurity standards. The tool aids in identifying gaps in security measures and helps in documenting compliance efforts effectively.
Overview
About CMMC ROI
CMMC ROI is an advanced investment calculator and strategic planning tool created by BomberJacket Networks, a recognized C3PAO and service-disabled veteran-owned business. Tailored specifically for Department of Defense (DoD) contractors, CMMC ROI addresses the complex challenge of navigating the mandatory Cybersecurity Maturity Model Certification (CMMC) requirements. This tool not only helps contractors understand compliance costs but also quantifies the financial return and strategic advantages associated with their investments. By analyzing factors such as company size, DoD revenue, required CMMC level, and current compliance status, CMMC ROI provides a detailed financial projection, including a 5-year cost estimate, payback period, and potential ROI. This empowers business leaders to make informed decisions as they prepare for the critical Q4 2025 enforcement deadline, ensuring the security of their DoD contracting future.
About Threat Watch
In an era where cyber threats are more sophisticated and frequent than ever, organizations are tasked with safeguarding their digital assets against a multitude of risks. Threat Watch is a cutting-edge cybersecurity intelligence solution designed to address this pressing challenge. With a focus on providing a unified view of your organization's cyber health, Threat Watch continuously analyzes assets, vulnerabilities, and exposures in real time. This tool is tailored specifically for IT security teams, risk managers, and business leaders who need to navigate the complexities of cybersecurity. Its main value proposition lies in speed and clarity; by automating assessments and prioritizing risks, Threat Watch transforms overwhelming data into actionable insights. Instead of becoming bogged down by endless alerts and manual processes, security teams can swiftly identify, understand, and mitigate threats, shifting from a reactive stance to a proactive strategy. Ultimately, Threat Watch turns cybersecurity from a daunting burden into a strategic advantage, empowering organizations to safeguard their critical assets efficiently.
Frequently Asked Questions
CMMC ROI FAQ
What is the primary function of CMMC ROI?
CMMC ROI serves as an investment calculator and strategic planning tool designed to help DoD contractors understand the costs and returns associated with achieving compliance with the CMMC requirements.
How does CMMC ROI calculate ROI?
The tool calculates ROI by analyzing protected contract values, including potential breach cost avoidance and competitive advantages, allowing businesses to see the financial impact of compliance investments.
Can I input my own data into the CMMC ROI tool?
Yes, CMMC ROI allows users to enter their unique company metrics, such as size and annual DoD revenue, to generate personalized financial scenarios that reflect their specific circumstances.
Why is CMMC compliance important for contractors?
CMMC compliance is critical for DoD contractors as it not only protects sensitive information but also enhances competitive standing in the market, reducing the risk of losing contracts and improving win rates against non-certified competitors.
Threat Watch FAQ
What types of threats can Threat Watch identify?
Threat Watch can identify a wide range of threats, including compromised credentials, unpatched software vulnerabilities, phishing attempts, and dark web exposures. This comprehensive approach ensures that organizations are aware of their security risks.
How does Threat Watch automate risk prioritization?
Threat Watch uses advanced algorithms to evaluate the severity and potential impact of identified vulnerabilities. By analyzing various factors, it automatically ranks risks, allowing teams to focus on addressing the most critical issues first.
Is Threat Watch suitable for small businesses?
Absolutely. Threat Watch is designed to scale with organizations of all sizes. Its user-friendly interface and automated features make it accessible for small businesses that may not have extensive security resources.
How does Threat Watch support compliance efforts?
Threat Watch supports compliance by continuously monitoring security measures and identifying gaps that could lead to non-compliance. It also provides detailed reporting, which is crucial for demonstrating adherence to regulations and standards.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a sophisticated investment calculator and strategic planning tool specifically designed for Department of Defense (DoD) contractors navigating the complexities of Cybersecurity Maturity Model Certification (CMMC) requirements. As an essential resource for businesses seeking to secure DoD contracts with confidence, CMMC ROI helps users quantify the financial return on their compliance investments. Users often seek alternatives to CMMC ROI due to various factors such as pricing, differing features, or specific platform needs. When choosing an alternative, it's important to look for tools that provide comprehensive financial analysis, customizable features, and user-friendly interfaces. Ensuring that the solution effectively meets compliance requirements while aligning with your organization's size and revenue is crucial for making informed decisions.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence solution that provides organizations with real-time insights into their security posture. It belongs to the business intelligence category, focusing on helping IT security teams and risk managers identify and mitigate potential threats efficiently. Users often seek alternatives due to various reasons, including pricing concerns, specific feature requirements, and the need for integration with existing platforms. When evaluating alternatives, it's crucial to consider factors such as usability, scalability, and the comprehensiveness of threat detection and response capabilities to ensure that the chosen solution aligns with organizational needs.
