Email List Cleaner vs RocketShare
Side-by-side comparison to help you choose the right tool.

Email List Cleaner
Clean your email list for free with privacy-first validation that happens in your browser.
Last updated: March 1, 2026
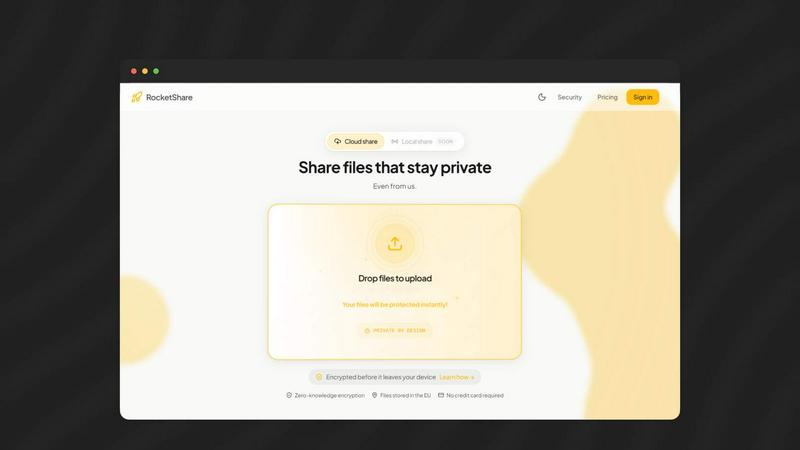
RocketShare
Share files with complete privacy using encryption that even we cannot access.
Last updated: March 4, 2026
Visual Comparison
Email List Cleaner
RocketShare
Feature Comparison
Email List Cleaner
Privacy-First, Client-Side Validation
The cornerstone of Email List Cleaner is its uncompromising approach to data privacy. Almost the entire validation process happens directly inside your web browser. Your full email addresses are never transmitted to or stored on any external server. The only data that leaves your device is the domain part of an address, which is sent to Google's DNS service solely to verify the domain's existence and mail server configuration. This ensures your sensitive contact lists remain completely confidential and secure.
Comprehensive Syntax & Domain Validation
Email List Cleaner performs a two-step validation process to ensure accuracy. First, it checks the syntax of each address to confirm it follows the proper format for a valid email. Second, it verifies that the domain name (the part after the '@') is real and configured to accept emails by checking its DNS records. This combination effectively filters out typos, malformed addresses, and domains that don't exist, significantly reducing hard bounce rates.
Advanced Filtering Options
Beyond basic validation, the tool offers granular control over what constitutes a "clean" email address. You can choose to filter out disposable email addresses from temporary mail services, role-based addresses like info@ or sales@, and unlikely valid addresses such as '[email protected]'. These options help you target genuine, engaged individuals and improve the quality of your communication list.
Intelligent Duplicate Removal
Email List Cleaner smartly identifies and removes duplicate entries to keep your list lean. It goes beyond simple text matching by understanding provider-specific rules. For instance, it recognizes that for Gmail addresses, '[email protected]' and '[email protected]' are the same, as Gmail ignores dots in the local part. It also handles email tags (e.g., '[email protected]'), ensuring a truly deduplicated and accurate list.
RocketShare
Zero-Knowledge Encryption
This is the cornerstone of RocketShare's security model. Every file you share is encrypted locally on your device before it ever leaves for the internet. The encryption key remains solely with you, typically as part of the shareable link. This ensures that the servers only handle unreadable, encrypted data, making it technically impossible for RocketShare or any third party to access your files' contents. Your privacy is non-negotiable and architecturally guaranteed.
Dual Sharing Modes: Cloud & Local
RocketShare offers unparalleled flexibility with two distinct sharing methods. For convenience and accessibility, use Cloud Share to upload encrypted files to secure EU-based servers, allowing recipients to download at any time. For maximum speed and privacy in real-time collaboration, use Local Share (peer-to-peer), which creates a direct, encrypted connection between devices without the files ever touching an external server, giving you complete control over the data transfer.
EU-Based Data Storage
All data uploaded via the Cloud Share function is stored on servers located within the European Union. This provides users with the strong data protection and privacy regulations afforded by EU jurisdiction, offering an additional layer of legal security and peace of mind for businesses and individuals concerned with data sovereignty and compliance with strict privacy laws like the GDPR.
Private-by-Design Architecture
RocketShare's entire system is engineered from the ground up to protect user privacy. From client-side encryption and zero-knowledge protocols to secure data handling, every technical decision reinforces that your files are for your eyes only. The platform requires no credit card to start, minimizing data collection, and provides transparent resources like a security whitepaper, demonstrating a full commitment to its private-by-design philosophy.
Use Cases
Email List Cleaner
Boosting Email Marketing Campaign Performance
For marketers and small business owners, maintaining a high sender reputation is critical for inbox placement. By using Email List Cleaner before every campaign, you can systematically remove invalid, disposable, and role-based addresses that cause high bounce rates and spam complaints. This leads to better deliverability, higher open and click-through rates, and a greater return on investment for your marketing efforts, all while protecting your brand's credibility.
Preparing for a Critical Product Launch or Announcement
When launching a new product, service, or making an important company announcement, you need confidence that your message will reach your audience. Cleaning your list with this tool ensures that your announcement lands in the inboxes of real, valid contacts. It prevents wasted sends and ensures your communication resources are focused on engaging potential customers who can actually respond.
Maintaining a Healthy CRM or Mailing List Database
For sales teams, researchers, and community managers, a CRM or mailing list database is a vital asset that decays over time. Regularly sanitizing these lists with Email List Cleaner helps maintain data hygiene. It's a cost-effective way to audit contacts, remove obsolete entries, and ensure that your team's outreach efforts are directed toward accurate and active email addresses, improving productivity and connection rates.
Safeguarding Sensitive Contact Lists for Non-Profits and Researchers
Non-profit organizations, academic researchers, and professionals handling sensitive or confidential contact lists cannot risk exposing that data to third-party services. Email List Cleaner's client-side, privacy-first model is the perfect solution. It allows these users to validate and clean their lists for fundraising drives, survey distribution, or member communications with the absolute assurance that their data never leaves their control.
RocketShare
Legal Document Exchange
Law firms and legal professionals constantly exchange highly sensitive case files, contracts, and evidence. Using standard email or consumer cloud storage risks attorney-client privilege and compliance breaches. RocketShare allows lawyers to send these documents with the absolute confidence that the content is inaccessible to anyone except the intended recipient, maintaining confidentiality and meeting stringent legal industry standards for data protection.
Secure Client Deliverables for Creatives
Photographers and videographers need to deliver high-resolution galleries and raw footage to clients. These files are large and constitute valuable intellectual property. RocketShare enables fast, secure delivery where only the client with the correct link can access the files. The zero-knowledge model ensures that even RocketShare cannot view the creative work, protecting the artist's IP and the client's privacy throughout the process.
Confidential Healthcare Data Sharing
Healthcare providers, therapists, and research teams need to share patient records, lab results, and study data in compliance with regulations like HIPAA. RocketShare's encryption-before-upload and EU data storage provide a secure channel for this sensitive information, ensuring that patient confidentiality is never compromised and helping organizations maintain critical regulatory compliance during digital transfers.
Internal Business Collaboration
Teams working on confidential projects, financial reports, merger details, or proprietary R&D need a safe space to collaborate. RocketShare's local peer-to-peer sharing allows team members in the same office or on a secure call to transfer files directly between computers at high speed, with no copy ever stored on a cloud server, eliminating the risk of external data leaks during internal collaboration.
Overview
About Email List Cleaner
In the world of email marketing and communication, a bloated, inaccurate contact list is more than just a nuisance—it's a direct threat to your sender reputation, campaign effectiveness, and bottom line. Sending emails to invalid, disposable, or role-based addresses leads to high bounce rates, spam complaints, and wasted resources. The challenge is finding a reliable way to clean your list without compromising the privacy and security of your sensitive contact data. This is where Email List Cleaner provides the definitive solution. Email List Cleaner is a privacy-first, free, and open-source web application designed to validate and sanitize lists of email addresses. It tackles the core problem by performing rigorous syntax and domain validation checks to separate valid emails from invalid ones, all while ensuring that your actual email data never leaves your browser and is never stored or seen by any third party, including the tool's own creators. It is the essential tool for marketers, small business owners, non-profits, researchers, and anyone who manages an email list and values data hygiene, cost-effectiveness, and absolute privacy. Its core value proposition is delivering powerful, trustworthy email validation completely free of charge and with an uncompromising commitment to user privacy.
About RocketShare
In today's digital landscape, sharing sensitive files is a constant necessity, yet it's fraught with risk. Standard cloud services and email attachments create vulnerabilities, leaving confidential data exposed to breaches, unauthorized access, and even the platform providers themselves. The challenge is finding a solution that doesn't force you to choose between simplicity and ironclad security. RocketShare is the definitive answer. It is a secure file-sharing platform built on the uncompromising principle of zero-knowledge encryption. This means your files are encrypted on your own device before they are uploaded; only you hold the key, often embedded directly in the share link. Not even RocketShare can ever access your content. Designed for professionals and businesses who handle sensitive information—such as lawyers, healthcare providers, accountants, and creative agencies—RocketShare delivers enterprise-grade security in a beautifully simple, self-serve package. With flexible sharing options (both cloud-based and local peer-to-peer) and data stored securely within the EU, it ensures your intellectual property and private communications remain truly private, solving the core dilemma of secure collaboration in a connected world.
Frequently Asked Questions
Email List Cleaner FAQ
How does Email List Cleaner protect my privacy?
Email List Cleaner is designed with privacy as its core principle. The validation process runs almost entirely within your own web browser. Your complete email addresses are never sent to our servers or any other external service for processing. The only external check performed is a DNS lookup for the domain name (e.g., "example.com"), which is necessary to verify if the domain can receive mail. You can review this process yourself by checking the tool's open-source code.
What is the difference between "invalid" and "unlikely valid"?
An email address marked as "invalid" has failed a fundamental check, such as having incorrect syntax (e.g., missing an '@' symbol) or belonging to a domain name that does not exist or is not configured for email. An "unlikely valid" address looks technically correct (like "[email protected]") but uses a local part (the text before the '@') that is commonly associated with fake or placeholder sign-ups. You can choose to filter these out using the processing options.
Does the tool guarantee that an email marked "valid" is real and active?
No, and no third-party validation service can offer a 100% guarantee. Email List Cleaner confirms that an address is syntactically correct and belongs to a domain with properly configured mail servers. However, it cannot determine if the specific mailbox (e.g., "[email protected]") actually exists on that server without sending an email, which would violate privacy. A "valid" result means the address is formatted correctly and its domain is ready to receive mail.
Why should I filter out disposable or role-based email addresses?
Filtering these addresses improves the quality and engagement of your list. Disposable addresses are temporary and often used for one-time sign-ups, meaning your future emails will not be read. Role-based addresses (like info@, support@) are generic inboxes monitored by multiple people or teams, often leading to lower engagement rates for marketing or personal communication. Removing them helps you focus on reaching individual decision-makers and engaged subscribers.
RocketShare FAQ
How does zero-knowledge encryption work with RocketShare?
Zero-knowledge encryption means the encryption and decryption of your files happen exclusively on your device. When you upload a file, RocketShare's application on your computer or phone encrypts it first. The resulting encrypted data is then sent to our servers. The key to unlock this data is not stored with us; it is generated and kept by you, often within the share link itself. Since we never have the key, we can never access the original file content.
What is the difference between Cloud Share and Local Share?
Cloud Share involves uploading your encrypted file to RocketShare's secure servers in the EU. The recipient can then download it using the unique link you provide, at any time. Local Share (peer-to-peer) creates a direct, encrypted tunnel between your device and the recipient's device over the internet. The file transfers directly between you without ever being stored on our servers, offering maximum speed and an additional layer of privacy for real-time sharing.
Where is my data stored?
For files shared via the Cloud Share function, all encrypted data is stored on secure servers located within the European Union. This ensures your data is protected under the EU's robust data privacy regulations. For files shared via Local Share (peer-to-peer), the data never touches our servers; it travels directly between the sender's and recipient's devices.
Is RocketShare compliant with regulations like GDPR?
Yes. RocketShare is designed with compliance in mind. By employing a strict zero-knowledge encryption model where we cannot access user data, and by storing all cloud data within the EU, RocketShare helps users maintain compliance with stringent data protection regulations like the GDPR. However, users are always responsible for ensuring their specific use of the tool meets all applicable legal requirements for their industry and jurisdiction.
Alternatives
Email List Cleaner Alternatives
Email List Cleaner is a free, open-source tool in the email validation category. It performs essential checks on your contact list directly in your web browser to identify invalid addresses, ensuring your email campaigns remain effective and your sender reputation stays strong. Users often explore alternatives for various reasons. Some may require advanced features like bulk processing or integration with specific marketing platforms. Others might be looking for a different pricing model, such as a paid service with dedicated support, or need validation capabilities that go beyond basic syntax and domain checks. When evaluating other email cleaning solutions, key considerations include the tool's approach to data privacy, the comprehensiveness of its validation methods, and its overall cost structure. It's crucial to find a balance between functionality, security, and value that aligns with your specific list management needs.
RocketShare Alternatives
RocketShare is a secure file-sharing platform in the productivity and management category, built on a zero-knowledge encryption model. This means files are encrypted on the user's device before upload, ensuring that no one else, including the service itself, can ever access the content. Users often explore alternatives for various practical reasons. These can include budget constraints, the need for specific collaboration features like real-time editing or user management, or a requirement for a different platform or storage location. Some may also seek simpler tools without advanced security or prefer a different pricing structure. When evaluating an alternative, consider your core priorities. Key factors are the level of security and privacy offered, the maximum file size and storage limits, the ease of use for both sender and recipient, and where your data is physically stored and processed. Balancing these elements against your budget will help you find the right fit for your needs.